In today’s digital era, secure software development is not just an option; it’s a necessity. As cyber threats evolve and become more sophisticated, the need to integrate security measures throughout the software development lifecycle is more pressing than ever. This guide explores the significance of secure software development, essential practices to adopt, and how Aibuzz.net can help you build resilient and secure software solutions.
What is Secure Software Development?

Secure software development is the process of designing, coding, and deploying software with security in mind. Unlike traditional development approaches where security is an afterthought, secure software development integrates security practices at every stage—from requirements gathering to deployment and maintenance. This proactive approach helps identify and mitigate potential security risks early, reducing vulnerabilities and ensuring robust protection against cyber threats.
Why is Secure Software Development Important?

- Protection Against Cyber Threats: Cyberattacks are constantly evolving, targeting software vulnerabilities to steal data or cause disruption. Secure software development minimizes these risks by identifying and addressing security flaws early in the development process.
- Data Integrity and Privacy: Ensuring the security of sensitive user data is crucial for maintaining trust and complying with data protection regulations such as GDPR and CCPA.
- Cost Efficiency: Fixing security issues during the development phase is significantly more cost-effective than patching them after deployment.
- Regulatory Compliance: Many industries have strict regulatory requirements related to software security. Integrating secure development practices helps in maintaining compliance with these standards.
- Brand Reputation: A security breach can severely damage a company’s reputation. Secure software development protects your brand’s integrity by reducing the chances of a security incident.
Key Principles of Secure Software Development
- Shift-Left Security: Security should be integrated early in the development lifecycle. By identifying and addressing vulnerabilities at the coding stage, developers can minimize security risks and reduce remediation costs.
- Secure Coding Practices: Adopting secure coding guidelines, such as input validation, output encoding, and proper error handling, reduces vulnerabilities like SQL injection, cross-site scripting (XSS), and buffer overflows.
- Threat Modeling: Threat modeling helps identify potential security threats and vulnerabilities by anticipating how malicious actors might exploit the system.
- Continuous Security Testing: Regular security testing, including static analysis, dynamic analysis, and penetration testing, ensures vulnerabilities are identified and fixed promptly.
- Automated Security Tools: Implementing automated tools for security testing, code review, and vulnerability scanning streamlines the secure software development process.
- Secure Deployment: Ensuring secure deployment configurations and regular updates to libraries and dependencies reduces exposure to known vulnerabilities.
- Access Control and Authentication: Implementing strong access controls and multi-factor authentication mechanisms prevents unauthorized access to sensitive data and systems.
Secure Software Development Lifecycle (SSDLC)
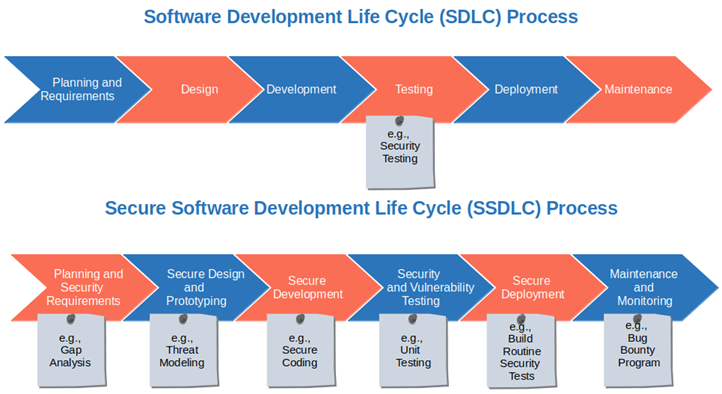
A Secure Software Development Lifecycle (SSDLC) integrates security practices into each phase of the software development lifecycle. Here’s how it works:
- Requirements Gathering: Identify security requirements early, including compliance needs, data security, and threat models.
- Design Phase: Incorporate secure architecture design, threat modeling, and risk analysis.
- Development Phase: Adopt secure coding practices and conduct static code analysis.
- Testing Phase: Perform security testing, including vulnerability assessments, penetration testing, and dynamic analysis.
- Deployment Phase: Ensure secure deployment configurations, including access controls and network security measures.
- Maintenance and Monitoring: Continuously monitor for vulnerabilities, apply patches, and conduct periodic security audits.

Best Practices for Secure Software Development

- Adopt DevSecOps Culture: DevSecOps integrates security into DevOps practices, promoting collaboration between development, security, and operations teams.
- Use Secure Libraries and Frameworks: Always use trusted and updated libraries and frameworks to minimize third-party vulnerabilities.
- Encrypt Sensitive Data: Ensure data is encrypted in transit and at rest to protect against data breaches.
- Perform Code Reviews: Peer code reviews help identify security flaws that automated tools might miss.
- Security Training for Developers: Regular security awareness training for developers ensures they are well-versed in secure coding practices.
- Incident Response Planning: Have a robust incident response plan to quickly mitigate security incidents and reduce their impact.
Tools for Secure Software Development
- Static Application Security Testing (SAST): Tools like SonarQube and Checkmarx analyze source code to detect security vulnerabilities.
- Dynamic Application Security Testing (DAST): Tools like OWASP ZAP and Burp Suite perform runtime analysis to find security flaws.
- Dependency Scanners: Tools like Snyk and Dependabot help identify vulnerabilities in third-party libraries and dependencies.
- Container Security: Tools like Aqua Security and Twistlock ensure secure container configurations and prevent container-based attacks.
- CI/CD Integration: Integrate security testing tools within CI/CD pipelines for continuous security validation.
How Aibuzz.net Ensures Secure Software Development
At Aibuzz.net, we understand the importance of building secure and reliable software solutions. Our team of experienced developers and security experts follow industry best practices and implement advanced security measures throughout the software development lifecycle. Here’s how we do it:
- Comprehensive Security Assessment: We conduct thorough security assessments, including threat modeling, vulnerability scanning, and penetration testing.
- Secure Coding Standards: Our developers adhere to secure coding guidelines to minimize vulnerabilities.
- Continuous Monitoring and Updates: We provide continuous monitoring services to detect and respond to emerging threats promptly.
- DevSecOps Integration: By integrating security into our DevOps practices, we ensure continuous security validation at every stage of the development process.
- Compliance Assurance: We ensure our software solutions comply with industry regulations, including GDPR, HIPAA, and PCI DSS.
Conclusion
In a world where cyber threats are constantly evolving, secure software development is more critical than ever. By adopting a proactive approach and integrating security at every stage of the software development lifecycle, organizations can safeguard sensitive data, maintain regulatory compliance, and protect their brand reputation.
At Aibuzz.net, we specialize in delivering secure software solutions tailored to meet your business needs. Our team of experts is committed to implementing the latest security practices and technologies to ensure your software remains resilient against cyber threats.
Contact us today at Aibuzz.net to learn more about our secure software development services and how we can help you build reliable and secure software solutions.

Leave a Reply