The healthcare industry is undergoing a remarkable transformation in 2025, with the rise of innovative technologies shaping the future of healthcare software development. From artificial intelligence (AI) to telemedicine, the demand for smarter, more efficient software solutions is on the rise. This blog explores the latest trends, challenges, and opportunities in healthcare software development and how they are revolutionizing the healthcare landscape.
The Importance of Healthcare Software in 2025
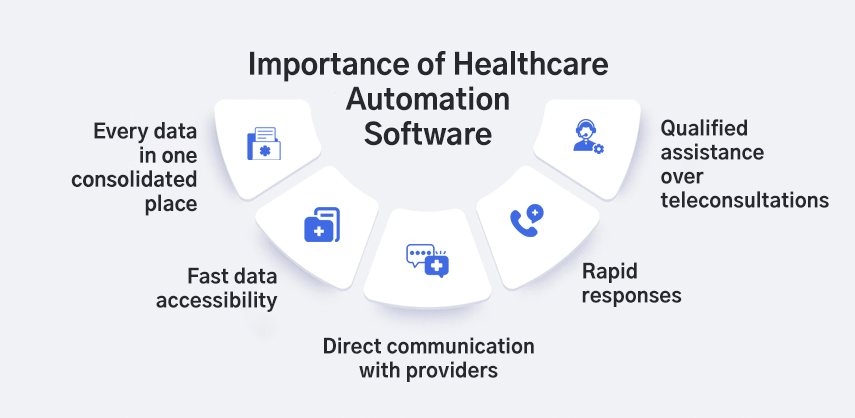
In 2025, healthcare software development will be more crucial than ever. As the industry embraces digitalization, healthcare software is becoming a cornerstone for improving patient care, optimizing operational efficiency, and ensuring data security. With the ever-growing need for seamless healthcare systems, developers are creating platforms that cater to a wide range of needs—from electronic health records (EHR) management to telemedicine solutions and predictive healthcare analytics.
The integration of healthcare software solutions will lead to:
- Improved Patient Outcomes: With real-time data analytics and predictive algorithms, healthcare providers can better understand patient needs and offer personalized treatments.
- Cost Efficiency: Healthcare software solutions streamline administrative tasks and clinical workflows, saving time and reducing costs.
- Enhanced Data Security: Software solutions built with robust security measures ensure the privacy and confidentiality of patient data, a vital concern in the healthcare industry.
Key Trends Shaping Healthcare Software Development

Healthcare software development in 2025 will be significantly impacted by emerging technologies. Here are some key trends that are driving the evolution of healthcare software:
1. Artificial Intelligence and Machine Learning
AI and machine learning are rapidly transforming healthcare software development. These technologies can analyze vast amounts of data, uncover patterns, and assist in decision-making processes. In 2025, healthcare software powered by AI and machine learning will become more advanced, with the ability to:
- Predict Health Outcomes: AI-driven software will use predictive analytics to forecast patient outcomes, enabling healthcare providers to take preventive actions.
- Automate Routine Tasks: AI will be used to automate administrative tasks, such as appointment scheduling, billing, and inventory management, allowing healthcare professionals to focus more on patient care.
- Enhance Diagnostics: Machine learning algorithms will assist in the diagnosis of diseases by analyzing medical imaging data and identifying abnormalities faster and more accurately than human doctors.
2. Telemedicine and Remote Patient Monitoring
Telemedicine has gained significant traction in recent years, especially after the global pandemic. By 2025, the demand for telemedicine solutions will continue to grow as healthcare providers adopt digital tools to offer remote consultations and monitor patient health from a distance.
Healthcare software solutions will integrate telemedicine features such as:
- Video Consultations: Software platforms will enable real-time video consultations, allowing patients to connect with healthcare professionals from the comfort of their homes.
- Remote Monitoring: Patients with chronic conditions will be able to use wearable devices and health tracking apps that integrate with healthcare software for continuous monitoring of vital signs like blood pressure, heart rate, and glucose levels.
- AI-driven Alerts: Telemedicine platforms will leverage AI to analyze patient data from remote monitoring devices and send automated alerts to healthcare providers when there are signs of health deterioration.
3. Blockchain Technology for Healthcare Data Security
With healthcare becoming increasingly digitized, data security remains a top concern. The use of blockchain technology in healthcare software development will be a game-changer in 2025.
Blockchain provides an immutable and transparent ledger that can be used to securely store and transfer healthcare data. Key benefits include:
- Decentralized Data Storage: Blockchain allows for the secure storage and sharing of medical records across multiple platforms without the risk of data manipulation.
- Increased Transparency: Blockchain ensures that all transactions and data exchanges are traceable, which is crucial for regulatory compliance and auditing.
- Enhanced Patient Privacy: By using blockchain, healthcare software can provide patients with greater control over their personal health data, ensuring that only authorized parties can access sensitive information.
4. Cloud Computing and Interoperability
Cloud computing will continue to play a significant role in healthcare software development. Cloud-based healthcare solutions offer flexibility, scalability, and cost-effectiveness, allowing healthcare organizations to store, access, and share data across multiple platforms. By 2025, healthcare software will be designed with a focus on:
- Data Sharing and Collaboration: Cloud computing enables seamless data sharing between healthcare providers, specialists, and patients, improving collaboration and patient care.
- Interoperability: One of the key challenges in healthcare is ensuring that various systems can communicate with each other. Cloud-based solutions in 2025 will prioritize interoperability, enabling healthcare organizations to connect EHRs, laboratory systems, and other essential software solutions.
5. Wearable Technology Integration
Wearable devices, such as smartwatches and fitness trackers, have become popular tools for monitoring health. In 2025, wearable technology will be fully integrated with healthcare software, providing real-time health data to both patients and healthcare providers. Some examples of wearable technology integration include:
- Continuous Health Monitoring: Wearables will track vital signs such as heart rate, blood oxygen levels, and sleep patterns, sending the data directly to healthcare providers for continuous monitoring.
- Chronic Disease Management: Patients with chronic diseases like diabetes and hypertension will benefit from wearable devices that provide real-time feedback, helping to manage their conditions more effectively.
- Personalized Health Insights: Healthcare software will use data from wearables to offer personalized recommendations based on individual health patterns, allowing patients to take a more proactive approach to their health.
Challenges in Healthcare Software Development

While the future of healthcare software development is promising, there are still several challenges that developers must overcome to ensure the successful implementation of these solutions:
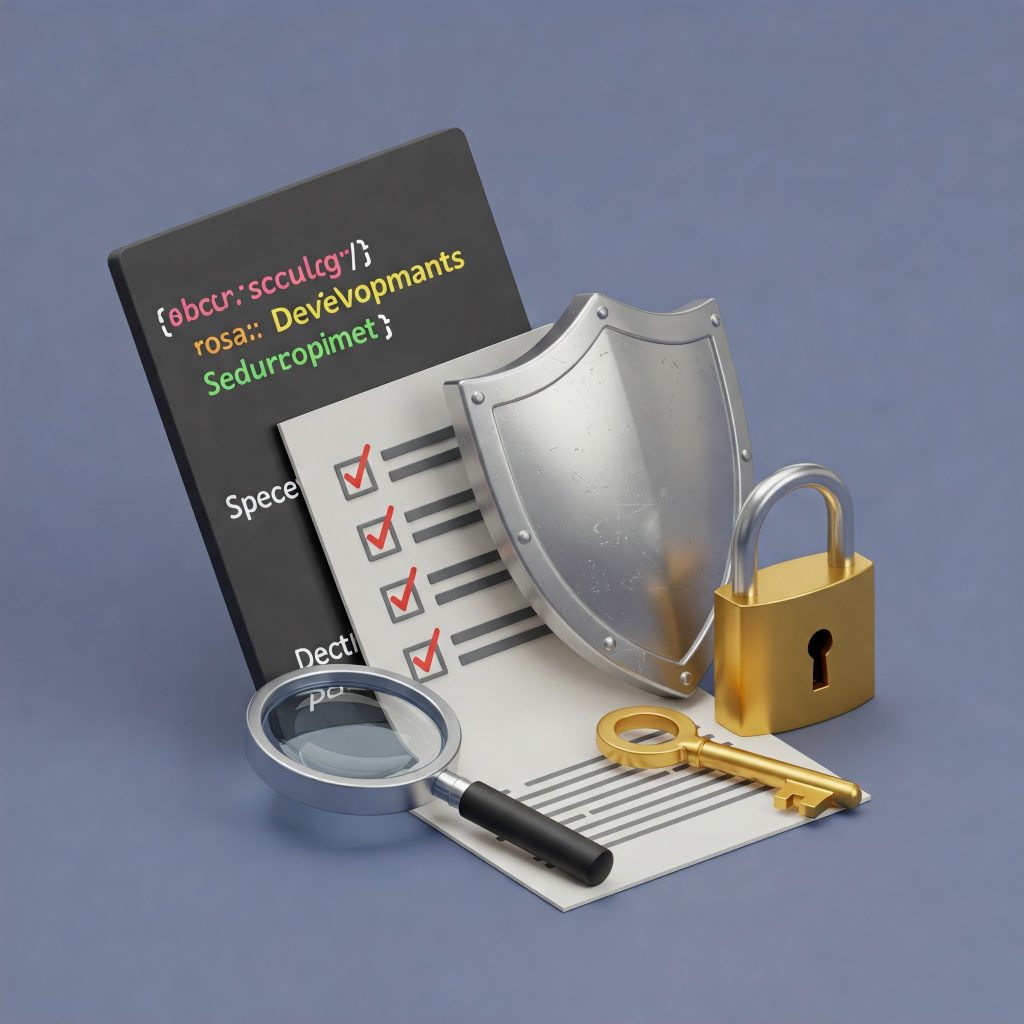
1. Data Privacy and Security
With the increasing volume of sensitive patient data being collected and stored, data security remains a primary concern. Healthcare software must adhere to strict regulations such as HIPAA (Health Insurance Portability and Accountability Act) to ensure that patient data is kept private and secure.
2. Regulatory Compliance
Healthcare software must comply with various regulations and standards, such as HIPAA, FDA (Food and Drug Administration) regulations, and GDPR (General Data Protection Regulation). Navigating these complex legal requirements can be challenging for developers, but it is essential to ensure that the software is legally compliant.
3. User Adoption
Despite the many benefits of healthcare software, some healthcare professionals and patients may resist adopting new technologies. Developers must focus on creating user-friendly interfaces and providing adequate training to ensure smooth adoption.
Conclusion: Embracing the Future of Healthcare Software Development
The healthcare industry is poised for significant transformation in 2025, thanks to advancements in technology that are reshaping healthcare software development. From AI-powered predictive analytics to blockchain-enhanced security, the future of healthcare software is bright and full of promise. However, challenges such as data security, regulatory compliance, and user adoption will need to be addressed for successful implementation.
At Aibuzz.net, we are committed to developing innovative healthcare software solutions that help organizations provide better patient care, enhance operational efficiency, and ensure data security. If you’re ready to embrace the future of healthcare software, get in touch with us today!
Call to Action: Let’s Shape the Future of Healthcare Together!
Partner with Aibuzz.net to develop cutting-edge healthcare software that will revolutionize patient care and healthcare management. Contact us today to learn more about how we can help you build software solutions tailored to your needs.
Contact:- 91 9967940928
Visit:- www.aibuzz.net
Mail us:- info@aibuzz.net