Introduction
Creating an advertising strategy from scratch is essential for businesses that want consistent growth, better brand visibility, and measurable results. Advertising without a strategy often leads to wasted budgets, unclear messaging, and low conversions.
This blog provides a step-by-step, informational guide to help beginners, marketers, and business owners understand how to plan and execute advertising campaigns effectively. Each step is written in simple language, making it easy to apply in real-world scenarios.
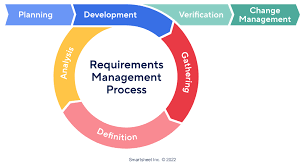
What Is an Advertising Strategy?
An advertising strategy is a structured plan that outlines how, where, and why a business promotes its products or services using paid media. It ensures that every advertisement aligns with business goals and reaches the right audience.
A strong strategy focuses on:
- Clear objectives
- Targeted audience reach
- Consistent brand messaging
- Measurable outcomes
Without planning, advertising becomes random and ineffective.
Why Building an Advertising Strategy from Scratch Matters

Starting from scratch allows businesses to design campaigns that are customized, data-driven, and scalable.
Key benefits include:
- Better control over advertising spend
- Improved audience targeting
- Higher conversion rates
- Clear performance tracking
- Long-term brand consistency
A structured approach ensures that every ad contributes to business growth.
Step-by-Step Guide to Build an Advertising Strategy from Scratch
Step 1: Define Advertising Goals
Every advertising strategy begins with clearly defined goals.
Common Advertising Goals
- Increase brand awareness
- Drive website traffic
- Generate qualified leads
- Boost online sales
- Retain existing customers
Your goals should follow the SMART framework to remain measurable and realistic.
Step 2: Understand Your Target Audience
Audience research is the foundation of a successful advertising strategy from scratch.
Important Audience Factors
- Demographics (age, gender, location)
- Interests and lifestyle
- Online behavior
- Problems and needs
Creating buyer personas helps you deliver ads that feel relevant rather than promotional.
Internal Link:
Learn more about audience targeting in our Digital Marketing Services/digital-marketing-services/
Step 3: Research Competitors and Industry Trends
Competitor analysis helps you understand market expectations and advertising standards.
What to Analyze
- Platforms competitors advertise on
- Messaging and tone
- Ad formats and visuals
- Engagement levels
External DoFollow Link:
Google Ads Transparency Center
https://adstransparency.google.com/
This resource helps you view real ads running across industries.
Step 4: Select the Right Advertising Channels
Choosing the right platforms ensures maximum visibility and engagement.
Popular Advertising Channels
Digital Advertising
- Google Search and Display Ads
- Social Media Ads (Facebook, Instagram, LinkedIn)
- YouTube Video Ads
Traditional Advertising
- Print media
- Outdoor advertising
- Radio and television
Platform selection should always be based on audience behavior, not trends.
Internal Link:
Explore our Advertising Services/advertising-services/
Step 5: Craft a Clear Advertising Message
Your message should communicate value, not just information.
Elements of an Effective Ad Message
- Attention-grabbing headline
- Clear problem-solution approach
- Unique selling proposition (USP)
- Emotional or logical appeal
- Strong call-to-action (CTA)
Examples of CTAs:
- Learn More
- Get Started Today
- Book a Free Consultation
Step 6: Plan and Allocate Your Advertising Budget
Budgeting plays a critical role in campaign success.
Budget Planning Tips
- Start with a test budget
- Divide budget by channel
- Track cost per click (CPC)
- Adjust spending based on results
External DoFollow Link:
HubSpot Marketing Statistics
https://www.hubspot.com/marketing-statistics
This data helps businesses make informed budget decisions.
Step 7: Design High-Quality Ad Creatives
Visual appeal directly affects engagement and click-through rates.
Creative Best Practices
- Use high-quality images or videos
- Keep text short and readable
- Maintain consistent branding
- Optimize creatives for mobile devices
Rich Media Resource:
YouTube – Digital Advertising Basics
https://www.youtube.com/watch?v=9No-FiEInLA
Step 8: Launch, Test, and Optimize Campaigns
Once live, continuous optimization is essential.
What to Test
- Headlines and descriptions
- Visual creatives
- Audience segments
- CTA placement
A/B testing helps identify high-performing elements and improves ROI.
Step 9: Track Performance and Key Metrics
Tracking ensures your advertising strategy from scratch remains effective.
Key Advertising Metrics
- Impressions
- Click-through rate (CTR)
- Conversion rate
- Cost per lead (CPL)
- Return on ad spend (ROAS)
Internal Link:
Learn more about Marketing Analytics Solutions/marketing-analytics/
Common Mistakes to Avoid
- Skipping audience research
- Setting unclear objectives
- Ignoring analytics
- Using identical ads across platforms
- Failing to optimize campaigns
Avoiding these mistakes improves campaign efficiency.
Future Trends in Advertising Strategy
Advertising continues to evolve with:
- AI-driven targeting
- Personalized ad experiences
- Short-form video advertising
- Privacy-focused marketing
Adapting to these trends keeps strategies relevant and effective.
Frequently Asked Questions (FAQs)
What does an advertising strategy from scratch include?
It includes goal setting, audience research, platform selection, budgeting, creative design, and performance tracking.
Is an advertising strategy necessary for small businesses?
Yes, it helps small businesses maximize limited budgets and target the right audience.
How long does it take to see results?
Paid ads may show results within days, while optimization improves performance over time.
Can beginners create an advertising strategy?
Yes, with clear steps and consistent testing, beginners can create effective strategies.
Conclusion
Building an advertising strategy from scratch helps businesses advertise with purpose, clarity, and measurable results. A well-planned strategy ensures that advertising is not just an expense, but a powerful growth tool.
By following structured steps and continuously optimizing, businesses can achieve sustainable advertising success.
Call to Action
Looking to build a high-performing advertising strategy?
Discover our expert-led Advertising and Marketing Solutions and start growing today.
☎️ 919967940928
✉︎ http://aibuzz.net
🌐 https://aibuzz.net/